Files on a computer are the electronic version of paper files that would lie stacked up to eye-level height on an office desk or take up endless cabinets in a chilled records room in the 40s. Like paper documents, files are ways of storing and passing information along. In computer terms, they are durable in that they exist beyond the running of a current program.
Today, almost all operating systems organizes their files into one-dimensional arrays of bytes. The format of a file can be found by looking at it's file extension - e.g. .jpegs are images and .txt are text files. Many programs have file extensions entirely their own, but file formats created by the most popular programs are usually widely supported. For example, a Microsoft Word .doc file can be read by many non-Microsoft programs. Most file formats also keep a few bytes for tracking basic information about themselves, such as creation dates, last edit dates, size, etc. This type of information is called metadata.
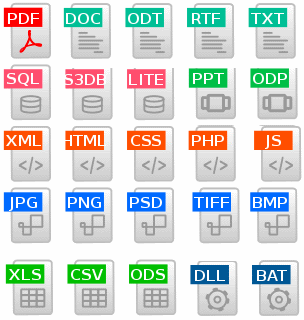
Example file extensions
The most fundamental two file operations are read and write. Reading here, simply means opening the file (you may have come across files marked as 'read-only' which is a way of preventing interference with the file's data) while writing means changing the contents of the file. Write operations are done at the time of saving a file which, with the recent move toward auto-saving, has become a very often and speedy occurrence. However, depending on the file format, one may also delete, move, grow, shrink, translate and perform many other types of operations on a file. When creating a program, it is important to keep in mind which operations will be needed in the files your program will be working with, so you can decide or create a suitable file type and system of manipulating them.
© BrainMass Inc. brainmass.com May 30, 2026, 6:42 am ad1c9bdddf