History
Almost as long as there have been wars, there have been spies, and as long as there has been spies, there has been cryptography. Pharaohs had cryptic messages inscribed on their tombs to impress, Ancient Chinese characters often hid secret meanings in their pictorial nature, the spies of early Indian rulers used sign language or vowel substitution in their correspondences and of course the Ancient Greeks developed tricks like the Caesar Shift and Polybius Square.
Most of these basic substitution/shift methods of cryptography were broken open upon the 9th century development of frequency analysis by Muslim nations combing the Koran for patterns. A man named Al-Kindi1 became effectively the first cryptanalyst by applying the known patterns in letter frequency to coded messages, allowing good guesses at which letters meant which. Thus began the ongoing battle between cryptography and cryptanalysis. Every advancement cryptography makes, cryptanalysis strives to meet, with varying success - Albertis' polyalphabetic substitution remained intact for 400 years2, Belaso's idea of a password is clearly still in use (albeit in a more advanced form), and Thomas Jefferson's wheel cipher was used right up to WW2.
Both fields of study became hotbeds of activity during WW2. Most famously, a 27-year-old Polish mathematician named Rejewski cracked the German Enigma Machine, and the UK's cryptanalysis efforts at Bletchley Park involved building Colossus, the world's first programmable, electronic computer, to speed the decryption of those Enigma messages. Already, the field was moving from being about linguistic skills to mathematics.
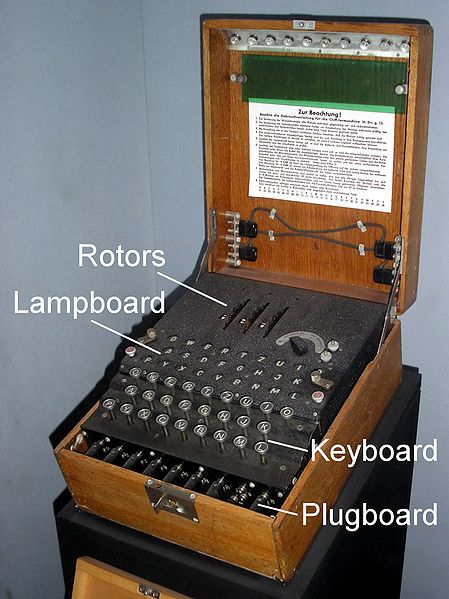
An Enigma Machine
Modern Cryptography
Now instead of encrypting letters, our cryptography is typically done on a binary level. Suddenly with computers, brute-force attacks on ciphers and the like that were previously too time-consuming to be practical can be done in minutes; critical numbers have to be hundreds of digits long to make up for the pure number crunching abilities of today's, and tomorrow's, machines.
The two overriding principles in security practice today are "security through obscurity" and Shannon's Maxim/Kerckhoff's Principle, "the enemy knows the system". The former is widely disparaged by computer scientists as it is analogous to going out and burying your fortune under a rock somewhere - only secure as long as no-one knows discovers the route to the rock. However, it does have some benefit in practice, at least in slowing down an attacker's preliminary information-gathering, and lesser-used application tend to experience fewer attacks simply because their inner-workings are not as publicly explored and documented. Reliable security comes from an appreciation of Shannon's Maxim, however, which proposes that a good security system holds even if the attacker understands the system completely - so long as the key is withheld.
The only method of cryptography that has been proven theoretically unbreakable is the rather impractical (though used by the KGB with some success) one-time pad. Many current cryptography methods with a reasonable level of security assured can be grouped under the following two types:
- Symmetric-key cryptography, e.g. the latest United States' NSA secure hash functions which use sponge functions3
- Public-key cryptography, e.g.the RSA algorithm for network security which uses the complexity integer factorization4
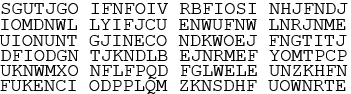
Sample excerpt from a 'page' of a one-time pad
References:
1. Alpen-Adria-Universität Klagenfurt (). The Breakthrough of Frequency Analysis. [ONLINE] Available at: http://cs-exhibitions.uni-klu.ac.at/index.php?id=279. [Last Accessed 15/04/2014].
2. Thawte (). A Brief History of Cryptography. [ONLINE] Available at: https://www.cryptochallenge.com/home/history. [Last Accessed 15/04/2014]
3. Bertoni, G., Daemen, J., Peeters, M. & Van Assche, G. (2008). Keccak in a nutshell. [ONLINE] Available at: http://keccak.noekeon.org/. [Last Accessed 15/04/2014].
4. Bimpikis, K. & Jaiswal, R. (). Modern Factoring Algorithms. [ONLINE] Available at: http://www.cs.columbia.edu/~rjaiswal/factoring-survey.pdf. [Last Accessed 15/04/2014].
© BrainMass Inc. brainmass.com June 28, 2024, 2:41 pm ad1c9bdddf